SonyEricssonJ120i » History » Revision 11
« Previous |
Revision 11/12
(diff)
| Next »
fixeria, 12/14/2023 11:12 AM
- Table of contents
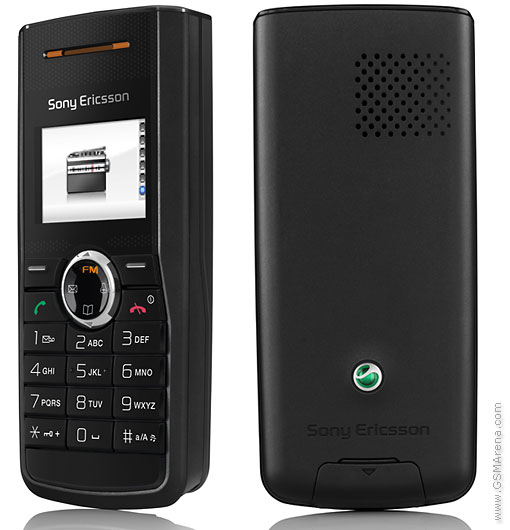
- Sony Ericsson J110/J120
Sony Ericsson J110/J120¶
This is another ODM phone model based on TI Calypso (most likely, by Chi-Mei). Not yet supported.
Both J110 and J120 are identical, except that the J120 has an FM receiver.
Specifications¶
https://www.gsmarena.com/sony_ericsson_j120-1843.php
- GSM 900/1800
- 99 x 44 x 17 mm, 75g
- STN 65k, 96 x 64
- 900mAh Li-Ion battery (BST-37)
Hardware¶
Large versions: SE-J110i-PCB.jpg, SE-J120i-PCB.jpg.
- DBB: D751749ZPH (well-known Calypso Lite)
- ABB: TI T3025BZQW (Iota)
- RF TRX: Si4210 (Silabs Aero II) - we don't support it
- RF PA: SKY77318-12 (similarly to SE K200)
- MX92U832ZCG (audio?)
Flash¶
- INTEL J030W[0D]YTQ2 (flash+RAM MCP)
- INTEL 28F320W18T (1.8 Volt Wireless Flash Memory, 4 MByte)
Flash dumps¶
- https://people.osmocom.org/fixeria/dump/se_j120i/J120i_R1A007_CXC1250845_Main.bin -- firmware, dumped using pstool
- https://people.osmocom.org/fixeria/dump/se_j120i/J120i_R1A007_CXC1250845_full.bin -- full flash, dumped using pstool
- https://people.osmocom.org/fixeria/dump/se_j120i/J120i-R1A007-CXC1250845-356325015955496-fc-full.bin -- full flash, dumped using fc-loadtool
Serial cable¶
J120i has the standard Sony Ericsson Fastport connector. Refer to SonyEricssonJ100i for more details.
Bootloader¶
Similarly to Sony Ericsson K200i and unlike Sony Ericsson J100i, J120i has the boot ROM (see CalypsoRomloader) enabled.
Stock firmware notes¶
Below are some notes related to the stock SE's firmware.
AT Modem mode¶
It's not yet known how to get access to the AT command interpreter.
Some AT commands can be found by running strings on the firmware dump.
$ strings J120i_R1A007_CXC1250845_Main.bin | grep "AT[*+]"
MMI codes¶
NOTE: for some codes you need to press the "green" (call) button.
- Standard SE codes:
-> * <- <- * <- *- service info and tests;<- * * <-- lock status;
Found in the firmware dump:
$ strings J120i_R1A007_CXC1250845_Main.bin | less ... *#06# F*#**837# *#**785# *#**664# *###664# *#**364# *#**364*564# *#**672# -- "OQC" menu (service tests) *#**372# -= "FQC" menu (service tests/info) *#**2263*0# -- BAND? *#**2263*1# *#**2263*2# *#**2263*3# *#**2263*4# *#**735*0# *#**735*12# *#**735*13# *#**833*2# *#**833*4# *#**833*7# *#**833*3# *#**778377# *#**464851# *#**324# *#**6360# F*#**6361# F*#**6362# F*#**6363# F*#**6364# F*#**266*0# *#**266*1# *#**277378# -- ASSERT? *#**636# *#**636*0# *#**636*1# *#**84637# *#**767# *#**3428*0# *#**3428*1# *#**3428*2# *#**778337# *#**25276# *#**62683# *#**3646633*0# *#**3646633*1# *#**678257# *#**33284# -- DEBUG
https://www.dcode.fr/t9-cipher is quite useful for guessing the purpose.
Updated by fixeria 5 months ago · 11 revisions

